NPTEL Cyber Security and Privacy Week 8 Assignment Solutions
NPTEL Cyber Security and Privacy Week 8 Assignment Answer 2023
1. Which of the following terms describes the process of making and using codes to secure the transmission of information?
- Algorithm
- Cryptography
- Steganography
- Cryptanalysis
Answer :- For Answer Click Here
2. What is term is used to describe a cryptographic method that incorporates mathematical operations involving both a public key and a private key to encipher or decipher a message?
- Private-key encryption
- Symmetric encryption
- Advanced Encryption Standard (AES)
- Asymmetric encryption
Answer :- For Answer Click Here
3. A substitution cipher that incorporates two or more alphabets in the encryption process is called——————-
- Monoalphabetic substitution
- Block cipher substitution
- Stream cipher substitution
- Polyalphabetic substitution
Answer :- For Answer Click Here
4. The current standard for the encryption of data, as specified by NIST ——— is based on the Rijndael algorithm, which was developed by Vincent Rijmen and Joan Daemen.
- DES
- RSA
- AES
- Message Digest
Answer :- For Answer Click Here
5. True or False:
Nonrepudiation means that customers or partners can be held accountable for transactions, such as online purchases, which they cannot later deny.
- True
- False
Answer :- For Answer Click Here
6. Limited-use symmetric keys for temporary communications during an online session is called
- Session keys
- One-time padding
- AES
- DES
Answer :- For Answer Click Here
7. Match the following
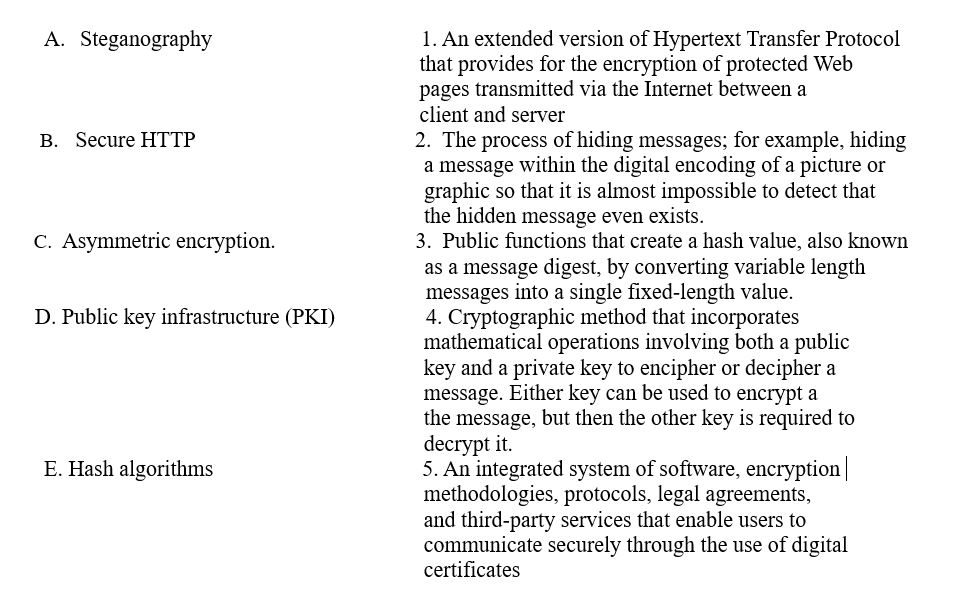
Choose the correct answer
- A-3, B-5, C-4, D-1, E-2
- A-2, B-1, C-4, D-5, E-3
- A-4, B-2, C-3, D-1, E-1
- A-5, B-2, C-3, D-1, E-4
Answer :- For Answer Click Here
8. Suppose that everyone in a group of N people wants to communicate secretly with the N-1 others using a symmetric key cryptographic system. Communication between any two persons should not be decodable by others in the group. The number of keys required in the system as a whole to satisfy the confidentiality requirement is
- 2N
- N(N-1)
- N(N–1)/2
- (N-1)2
Answer :- For Answer Click Here
9. Decrypt the following message if it was encrypted using a shift cipher with a shift of 3.
Message: NPTELINFORMATION
- Q S W H O L Q I R U P W L R Q
- Q S W H O L Q I T U P W L R Q
- Q S W F O L Q I R V P W L R Q
- Q S W H O L Q I R V P W L R Q
Answer :- For Answer Click Here
10. ————security protocols are used to protect e-mail
- SMTP
- HTTPS
- S/MIME, PEM, and PGP
- Telnet
Answer :- For Answer Click Here
11. What is the most popular encryption system used over the Web?
- Diffie Hellman key exchange
- RSA
- Block cipher
- DES
Answer :- For Answer Click Here
| Course Name | Cyber Security and Privacy |
| Category | NPTEL Assignment Answer |
| Home | Click Here |
| Join Us on Telegram | Click Here |